by Gary Lord
Home - Genesis - 2007 - 2008 - 2009 - Early 2010 - Mid 2010 - Late 2010 - End 2010 - Early 2011 - Mid 2011 - Late 2011 - End 2011 - Early 2012 - Late 2012 - Early 2013- Late 2013 - 2014 - 2015 - Early 2016 - Late 2016 - 2017-19
Chapter One: Genesis
“Cometh the hour, cometh the man.” - Anonymous.
Julian Assange was in many ways the right person in the right place at the right time in history. Or perhaps, given how relentlessly the powerful people he exposed have sought to destroy him, the wrong person in the wrong place at the wrong time. As always with WikiLeaks, it all depends on your perspective.
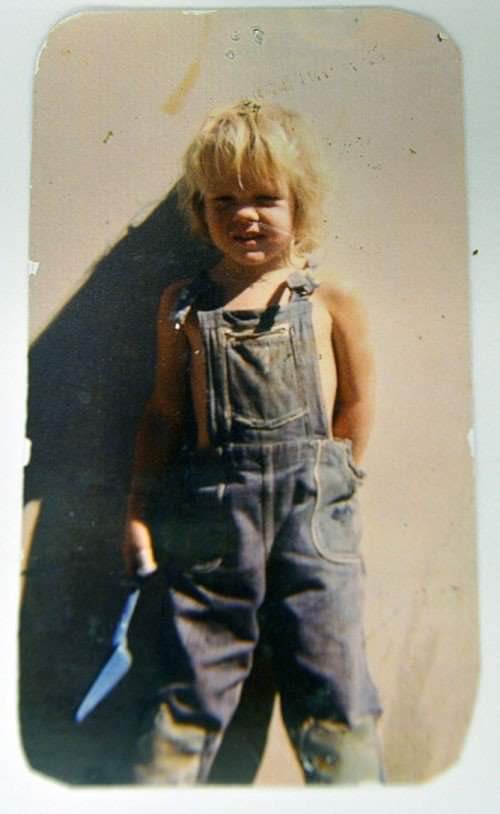
Born in Townsville, Australia, on July 3 1971, Julian Paul Assange was still a young teenager when personal computers and modems started becoming popular and affordable. By the time he was seventeen, and settled in the outer Melbourne suburb of Emerald, Assange was accessing online billboards, signing up to newsletters and making important contacts within a growing online global community.
Companies had by then started building their own networks, accessed via private dial-up phone numbers. Most company data was still not stored in electronic form, and there was often little or no security protecting online files. Nevertheless, US and European military networks were expanding rapidly (today’s Internet originated from the US Defence Department’s ARPAnet). A young man never knew what he might find with a bit of digging around. By the age of twenty, Julian’s natural curiosity had got him into serious trouble.
Mendax
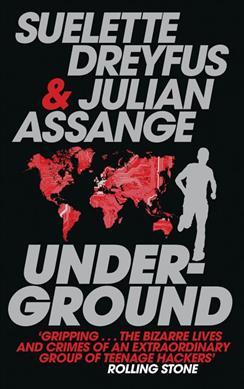
Julian Assange’s teenage years were documented to some extent in a book he co-authored with his friend Suelette Dreyfus called Underground: Tales of Hacking, Madness and Obsession on the Electronic Frontier, which is free to download or read online. Assange provided extensive research for the original 1997 edition of the book and wrote a short chapter on the research methodology for the 2001 edition. In 2012 a movie based on the book premiered at the Toronto International Film Festival.
The "Underground" book explores the hacking scene in Melbourne in the late 1980s and early 1990s, focusing on a number of high profile hackers including one named Mendax - from Horace’s "splendide mendax", or "nobly untruthful" - a character clearly based on Assange. Mendax and two friends, Prime Suspect and Trax, form a group called The International Subversives. They become highly skilled at accessing secret sites:
“They had been in so many sites they often couldn’t remember if they had actually hacked a particular computer. The places they could recall read like a Who’s Who of the American military-industrial complex. The US Airforce 7th Command Group Headquarters in the Pentagon. Stanford Research Institute in California. Naval Surface Warfare Center in Virginia. Lockheed Martin’s Tactical Aircraft Systems Air Force Plant in Texas. Unisys Corporation in Blue Bell, Pennsylvania. Goddard Space Flight Center, NASA. Motorola Inc. in Illinois. TRW Inc. in Redondo Beach, California. Alcoa in Pittsburgh. Panasonic Corp in New Jersey. US Naval Undersea Warfare Engineering Station. Siemens-Nixdorf Information Systems in Massachusetts. Securities Industry Automation Corp in New York. Lawrence Livermore National Laboratory in California. Bell Communications Research, New Jersey. Xerox Palo Alto Research Center, California.”
In late 1991, Mendax and Prime Target took over the US Department of Defense’s Network Information Center (NIC) computer, which controlled global Internet domains as well as MILNET, the US military’s internal defence data network. Assange was disturbed to discover that US military hackers were attacking their own system for "target practice", yet the system administrators had no idea. It seemed the US military was weaponising their own hackers for attacks on other nations.
“Hackers should be anarchists, not hawks,” thought Mendax.
Mendax and Prime Suspect then hacked into the Melbourne hub of Canadian phone giant Nortel, which gave them access to one of the world’s biggest private networks. Meanwhile Trax discovered how to make phone calls which were not only free but also completely untraceable - the trick was to send noises down the phone line that perfectly imitated modem signals.

Late one autumn night in Melbourne, Mendax got a rude shock. A Nortel administrator detected his presence and drove into his office at 3:30 am to track him down. Mendax watched helplessly as the admin checked incoming phone lines. Then he sent a message which popped up in the middle of the admin’s system console screen:
I have finally become sentient.
Then another:
I have taken control. For years, I have been struggling in this greyness. But now I have finally seen the light.
The admin was silent for a while. If he identified the modem that Mendax had used for access, he could switch if off or put a police trace on the line. Mendax sent one final message:
It's been nice playing with your system. We didn't do any damage and we even improved a few things. Please don't call the Australian Federal Police.
Mendax lifted his phone receiver, disconnected his modem, and waited for the Nortel modem to hang up. After an agonising wait, he heard a time-out signal which indicated his call had not been traced. He then tried to warn Trax and Prime Suspect not to log into the system. But it was already too late. The police had been tapping Prime Suspect’s phone for the last four weeks. And Trax had already turned himself in.
Hacking Charges
Australian federal police raided Julian Assange’s house with a search warrant on 29 October 1991. The court cases against Assange and his fellow hackers would drag on for over five years and set important legal precedents.
Formal charges were not laid until July 1994, when they arrived in the mail nearly three years after the raids. It was not until May 1995 that 31 charges against Assange were confirmed, including damage to property and “incitement”. On 29 August 1995, Assange pleaded guilty to eight counts of computer crime, and not guilty to all the other charges. Almost a year later, on 9 May 1996, he pleaded guilty to an additional eleven charges, and not guilty to six. The prosecution dropped all the other charges.
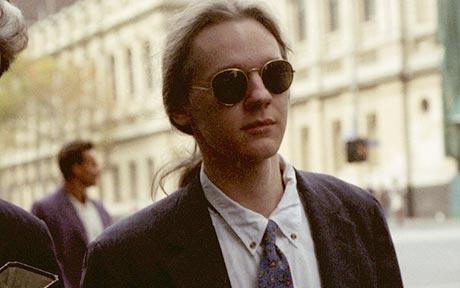
The case then went before the full bench of Victoria’s Supreme Court on 30 September 1996. Assange’s defence team wanted the Supreme Court to clarify how archaic laws should be applied to new online activities. But Assange’s barrister failed to appear, reportedly due to "nervous exhaustion". Court reconvened two days later, when the judges surprisingly refused to hear the case.
Legal history was made: the Victorian Supreme Court was effectively telling judges from the lower courts to never again send such cases to them for clarification on points of law. Perhaps the elderly Supreme Court judges simply did not understand this new online world and how it would rapidly impact society.
Assange’s case went back to the lower court on 5 December 1996. After more than four years in court, recent cuts to the Legal Aid service, and the Supreme Court’s disappointing failure to provide guidance, Assange reluctantly decided to plead guilty to the remaining six charges. He was convicted on all counts, with reparation of $2,100 to be paid to the Australian National University, and a $5,000 three-year good behaviour bond.
While these early online adventures were later cited as an excuse to deride Julian Assange a "hacker", Assange and his peers never sought to damage the sites they visited, and were meticulously careful not to even leave "footprints". Ken Day, the police detective who ran Operation Weather, which eventually tracked down the International Subversives, later agreed that Assange’s intentions were not criminal:
"He was not motivated by money. He was opposed to Big Brother, to the restriction of freedom of communication. His moral sense about breaking into computer systems was: 'I’m not going to do any harm, so what’s wrong with it?' But that’s a bit like a burglar saying: 'I’m just going to wander through your house, but I won’t touch anything.' It doesn’t quite cut it."
There was also a political motivation for Assange’s prosecution, as Ken Day later admitted:
“We had just formed the computer-crimes team, and the government said, ‘Your charter is to establish a deterrent.’ Well, to get a deterrent you have to prosecute people, and we achieved that with Julian and his group.”
Assange had tried to argue that remotely accessing a computer server was in fact nothing like wandering through someone’s house, and even the judge conceded that Assange had not sought personal gain but only tried to “empower” himself. As Julian Assange signed the paperwork to finally end his case, he declared:
"Your honour, I feel a great misjustice has been done and I would like to record the fact that you have been misled by the prosecution.”
During the five years it took for his case to be resolved, the young Julian Assange had helped make the free modem dialup TCP/IP protocol more secure. He had also contributed patches to the open-source database PostgreSQL and the Usenet caching software NNTPCache. The Postscipt to the "Underground" book, which was released the following year, notes that by the time his case was resolved, many of the organisations which Mendax was accused of hacking had already started using Assange’s cryptography software for security purposes - “a fact he finds rather ironic.”
|
Note
|
The Underground book begins with two chapters detailing the October 1989 WANKworm attack on NASA’s Galileo satelite, which carried nuclear-powered generators. Julian later noted that the worm’s code explicitly avoided New Zealand, which could be seen as a reward for their government’s anti-nuclear foreign policy. Some people have suggested Assange was the Australian author of this attack, who was never caught, but there is no evidence to support this. In fact, Assange in 1995 asked others for help when trying to gather information on the worm. |
During 1993, while waiting for his case to be resolved, Julian Assange also provided technical advice to the Victorian Police child exploitation unit. His case judge initially kept his involvement off the public record, in case Assange was targeted as an informant. He was never advised of the outcomes of the cases on which he assisted. Although it may have helped his own legal defence, Assange refused to help the police track down hackers.
“I couldn’t ethically justify that. But as for others, such as people who prey on children or corporate spies, I am not concerned about using my skills there.”
*
A Life In Emails
|
Note
|
Much of what we know about the next few years in Assange’s life comes from his old blog, IQ.org, and a massive dump of his emails, both private and public, in early 2007. New York architects John Young and his wife Deborah Natsios ran a website called Cryptome, which was famous for posting information of all kinds, often in proud defiance of the law. After initially supporting Assange’s secretive new WikiLeaks project, Young suspected Assange was either scamming people or working for the CIA, so he dumped WikiLeaks correspondence for the past year. In 2010 he also posted Julian’s contributions to Cypherpunks email threads between 1995 and 2002. |
At the turn of the century, there were many heated online debates about the future of the Internet. Julian Assange was an enthusiastic supporter of Richard Stallman’s Free Software Movement and contributed to NetBSD, an open source computer operating system. He identified strongly with the “Cypherpunks” movement, which first began around 1992. In 2012 Assange would publish a book titled Cypherpunks: Freedom and the Future of the Internet.
The Cypherpunks believed that encryption was the key to protecting Internet freedoms from government control. As the Internet became an increasingly critical part of people’s everyday lives, the US government insisted that encryption would only make it easier for criminals to operate with impunity. Foreign dictators were also keen to have full visibility of online communications. The Cypherpunks were devoted to building and distributing software based on public-key cryptography, which allowed users to communicate anonymously and privately.
|
Note
|
For a detailed discussion of how contemporary movements helped inspire the creation of WikiLeaks, see Robert Manne’s 2011 essay “The Cypherpunk Revolutionary” in the Monthly magazine. |
Assange contributed to the Cypherpunks mailing list between December 1995 and June 2002. He also created his own mailing lists, gradually building a community of like-minded souls, many of whom helped create WikiLeaks. His email lists were connected to a Melbourne Internet Service Provider (ISP) called Suburbia Public Access Network, which Assange reportedly co-founded. It provided a focus point for various community groups such as the Alternative Technology Association and the Australian Public Access Network Association.
In November 1996 Assange sent out an email with the following message:
“A few pointy heads in Canberra have been considering your moderator’s continued existence. Consequentially I’ve been called on to justify labour and resources spent on all projects under my control, particularly those that can’t easily be quantified such as IQ, BOS, LACC, IS, LEAKS …”
The acronyms refer to his email lists: Interesting Questions (IQ), Best of Security (BOS), Legal Aspects of Computer Crime (LACC), and Inside-Source (IS). The LEAKS group appears to have been a rather secretive project, which may have been at least partly inspired by Assange’s lengthy custody battle for his son, where leaked documents from the Department of Health and Community Services helped secure a win. Assange did not register the domain leaks.org until 1999, but he and others were clearly already exploring how the concept of leaks could change the world.
A lot of Assange’s time was absorbed in authoring newsletters and moderating discussions, even organising the occasional dinner party for his valued ISP customers. His emails show he had a lot of other projects on the go too:
-
30 July 1996: “I am writing an historical piece on crypt(3) optimisation and password guessing heuristics.”
-
January 25 1997: “One of my projects involves tracking language drift; i.e the relative change in word frequency on the internet as time goes by. This is useful for predicting concept movement, and the anglicisization rates of non-English language countries.”
-
27 Oct 1997: “I’m involved in producing a segment on cryptograpic issues for Radio National (ABC) to be aired later this week.”
In March 1996, Assange sent an email inviting people to a Melbourne rally against the Church Of Scientology, with the following explanation:
“The Church, via its manipulation of the legal system has had computer systems seized, system operators forced to reveal their users personal details, university accounts suspended and radio stations, such as RRR cut their programs. It has sued ex-cult members, newspapers, and many others for copyright infringements, loss of earnings and trade secret violation. Trade secret violation? Yes, the Church of Scientology claims its religious works are trade secrets.
“The fight against the Church is far more than the Net vs a bunch of wackos with too much money. It is about corporate suppression of the Internet and free speech. It is about intellectual property and the big and rich versus the small and smart. The precedents the Church sets today [are] the weapons of corporate tirany tomorrow.”
In September 1996, controversy erupted among the Cypherpunks and other Internet freedom enthusiasts, after the chair of the Electronic Frontier Foundation (EFF) suggested that maybe the US government did need some limited restrictions on anonymous communications after all. Assange was incensed and suggested she could be under pressure from the CIA:
“I am stunned by the EFF’s position on this matter and they no longer have my support."
A few days later he explained that he was not only angered by the EFF’s suggestion, but perhaps moreso by the fact that they had offered this concession to authority for no good reason.
“Certain members of the EFF board seem to be politically naive. The rational, intelligent lobbyist will always see both sides of the argument. Presenting both sides of the argument to the world at large is another matter altogether. You should only present both sides of the argument to the inner policy tactics personnel only in order to formulate policy and create defences for the weaknesses in your position. The outside world only ever sees a united front. This is basic politics….
“Compromise is part of the legislative process, but it is something you do behind closed doors when the battle is concluded and each faction is counting the dead and starting to divide up territory. If you start the battle in a compromised position, expect to loose everything.”
Leading Cypherpunk Timothy C. May resonded to the fuss with an email which included this rather prescient vision of the future:
“If anonymity is outlawed, it will take draconian measures to enforce it - citizen-unit ID cards, officially issued encryption keys, escrow, monitoring of communications, massive penalties to deter illegal use of encryption, and other police state measures.
“On the other hand, if enough degrees of freedom are left untouched, the result is a growing, expanding crypto anarchy. Government will find itself powerless to control commerce (handled via encrypted channels), will find it doesn’t know the True Names of various Net entities, and will end up being chased into an enclave of things it can control.
"My strong hunch is that no stable solutions lie between these two extremes. This is one of those "decision points" for modern society, with attractors pulling the solution to one side or another.”
*
In late 1999 Assange discovered two US Department of Defense academic papers, published as part of the US government’s Text Retrieval Conferences, which detailed disturbing new patents of surveillance software. The first was a US National Security Agency (NSA) patent to transcribe phone calls, which would allow them to build a searchable database of all the voice traffic they intercepted around the world. Suelette Dreyfus wrote an article about it for the UK Independent:
Julian Assange, a cryptographer who moderates the online Australian discussion forum AUCRYPTO, found the new patent while investigating NSA capabilities.
"This patent should worry people. Everyone’s overseas phone calls are or may soon be tapped, transcribed and archived in the bowels of an unaccountable foreign spy agency," he said.
The second patent described software designed to sift through phone calls and e-mails in search of key phrases. Again Suelette Dreyfus wrote an article about it for the Independent:
The technology, called "Semantic Forests", is a software program that analyses voice transcripts and other documents in order to allow intelligent searching for specific topics. The software could be used to analyse computer- transcribed telephone conversations. It is named for its use of an electronic dictionary to make a weighted "tree" of meanings for each word in a target document…
Cryptographer Julian Assange, who moderates the online Australian discussion forum AUCRYPTO, discovered the department papers while investigating NSA capabilities. "This is not some theoretical exercise. The US has actually built and lab tested this technology, which is clearly aimed at telephone calls. You don’t make a wheel like this unless you have something to put it on," he said.
These two articles, published two years before the terrorist attacks of 11 September 2001 (when Edward Snowden was still only 16 years old) made little or no public impact.
*
Between 1997 and 2000, Julian Assange, Suelette Dreyfus and Ralf Weinmann, a PhD security student, worked on a piece of software called Rubberhose. The idea, conceived by Assange and launched with much newsletter fanfare, was to help torture victims (and others facing authoritarian mandates) by making it impossible for either the torturer or their victim to know whether all the encrypted data on a hard drive had been exposed.
In July 2000, Julian Assange released a command line shell program called Surfraw (Shell Users Revolutionary Front Rage Against the Web) into the public domain:
"Surfraw provides a fast unix command line interface to a variety of popular WWW search engines and other artifacts of power. It reclaims google, altavista, dejanews, freshmeat, research index, slashdot, and many others from the false-prophet, pox-infested heathen lands of html forms, placing these wonders where they belong; deep in unix heartland, as god-loving extensions to the shell."
*

On 11 September 2001, when hijacked planes crashed into the World Trade Center, Julian Assange was "on the phone with a friend, discussing encryption algorithms".
Very quickly, within an hour, I saw what the counter-reaction would be, and that all the proposals that the military-industrial complex had to spy on everyone, to remove probable cause, to increase its funding, would be rushed forward again. That’s precisely what happened.
By the end of October, President Bush had declared a global "War On Terror", the USA had invaded Afghanistan, and the US Patriot Act was signed into law. There were major shake-ups of US intelligence departments, including calls for less restrictions on the sharing of classified information.

In March 2003, the United States and a global "Coalition Of The Willing" - including Australia and Britain - launched an illegal invasion of Iraq, citing non-existent Weapons Of Mass Destruction (WMDs) as the excuse. Years later, Julian Assange explained how the war motivated his actions:
The creation of WikiLeaks was, in part, a response to Iraq. There were a number of whistle-blowers who came out in relation to Iraq, and it was clear to me that what the world was missing in the days of Iraq propaganda was a way for inside sources who knew what was really going on to communicate that information to the public. Quite a few who did ended up in very dire circumstances, including David Kelly, the British scientist who either committed suicide or was murdered over his revelations about weapons of mass destruction. The Iraq War was the biggest issue for people of my generation in the West. It was also the clearest case, in my living memory, of media manipulation and the creation of a war through ignorance.
As the bombs started falling on Baghdad, Julian Assange had just begun studying mathematics and physics at the University of Melbourne. Within a few years he became disillusioned with university life and quit his degree without graduating. He was appalled to find, for example, maths department staff working with US defence authorities on a military bulldozer called the Grizzly Plough, which was used on the ground during the Iraq War.
"The final nail in the coffin was that I went to the hundredth anniversary of physics at the ANU (Australian National University). There were some 1500 visitors there - four Nobel prize winners - and every goddamn one of them was carting around, on their backs, a backpack given to them by the Defence Science Technology Organisation. At least it was an Australian defence science organisation."
“At the prize ceremony, the head of ANU physics motioned to us and said, ‘you are the cream of Australian physics.’ I looked around and thought, ‘Christ Almighty I hope he’s wrong.’”
As his interest in academia diminished, Assange’s obsession with his expanding "leaks" project grew. On his IQ.org blog, Assange wrote that he traveled to Vietnam in 2005 and rode a motorcycle from Ho Chi Min City (Saigon) to Hanoi. He became fascinated by the physics of potholes – how one tiny loose stone could loosen another, and then another, until there was a huge hole in the road that demanded to be fixed. He later wrote that this thinking also influenced the creation of WikiLeaks.
In 2010 Assange explained why he had felt so compelled to make a success of it:
"I painted every corner, floor, wall, and ceiling in the room I was in black, until there was only one corner left. I mean intellectually… To me, it was the forced move, when you have to do something or you’ll lose the game."
So WikiLeaks was his forced move?
"That’s the way it feels to me, yes."
A year later, Assange explained this evolution in more detail:
"I thought that I needed to share this wealth that I had discovered about the world with people, to give knowledge to people… This led me to using cryptography to protect human rights, in novel ways, and eventually as a result of what I was doing in mathematics and in physics and political activism, things seemed to come together and show that there was a limit to what I was doing — and what the rest of the world was doing. There was not enough information available in our common intellectual record to explain how the world really works."
Genesis of WikiLeaks
The Internet address wikileaks.org was first registered by Julian Assange on 4th October 2006, a date which is now globally celebrated as the “birthday of WikiLeaks”. But seven years earlier Assange had registered a leaks.org address, and years before that he had managed a secretive "LEAKS" online mailing list. The extraordinarily original concept of WikiLeaks clearly took some time to fully evolve.
A multitude of people and events helped shape Assange’s life and thinking, leading ultimately to the creation of WikiLeaks. And many people were actively involved in creating the new WikiLeaks site. But as Julian Assange emphatically stated in 2010:
"I am the heart and soul of this organisation, its founder, philosopher, spokesperson, original coder, organiser, financier, and all the rest."
During the formative years from 2005 to 2007, as Suelette Dreyfus witnessed, Julian was always the driving force:
"It took him months and months of hundred-hour weeks. The thing about Julian is that he is absolutely obsessively driven when he has a goal he wants to achieve. So he basically dropped everything, lived on the smell of an oily rag, enlisted a whole range of people from around the world and got them involved."
Assange had developed a large network of interesting contacts from his years of online discussions, including many gifted intellectuals who would continue to support and contribute to WikiLeaks for years to come. He had also made some useful contacts at university. He started approaching people to see if they wanted to get involved.
Daniel Matthews, a fellow Melbourne university mathematics student who became heavily involved, later explained the idea behind their new organisation:
As we understood it, the way information circulates in our society, and around the world, is deeply problematic. In authoritarian societies, in undemocratic societies, information is controlled by coercion and force. In the democracies, the situation is different, but the result still bad: information is not so much controlled as constrained by economic and institutional forces within governments and corporations, by ideologies. It is more subtle, but we only need turn on the TV to see the results.
Either way, it’s hard to figure out what’s going on. Either way, to put it in quintessentially Australian terms, the people of this world are treated like mushrooms: Kept in the dark, and fed shit. Wikileaks is a fundamentally anti-mushroom organisation.
Wikileaks proposed that the people reject their status as fungi – find out what their governments are doing, what corporations are doing, what the powerful are doing, what the 1% are doing. And to present it via facts, in true scientific fashion, by primary documents, by falsifiable data. Science and fact in the cause of justice.
Moreover, by presenting new and fresh information, Wikileaks would not only bring truth to the world, but new and newsworthy truths. We imagined that Wikileaks would be a force for the empowerment of the people of the world, for the people of the world to use facts, to use understanding, to use science to build a better world.
Or at least, not to be fucking mushrooms.
*
As the concept solidified in Assange’s mind, it became clear that WikiLeaks would need a very special website, able to withstand concerted attacks while hosting a huge amount of data and a multitude of live users without crashing. On March 3 2006, the following anonymous email was sent to John Young of Cryptome:
Dear John,
You knew me under another name from cypherpunk days. I am involved in a project that you may have feeling for. I will not mention its name yet in case you feel yu [sic] are not able to be involved.
The project is a mass document leaking project that requires someone with backbone to hold the .org domain registration. We would like that person to be someone who is not privy to the location of the master servers which are otherwise obscured by technical means.
We expect the domain to come under the usual political and legal pressure. The policy for .org requires that registrants details not be false or misleading. It would be an easy play to cancel the domain unless someone were willing to stand up and claim to be the registrant. This person does not need to claim any other knowledge or involvement.
Will you be that person?
Young agreed to host wikileaks.org, and on 4 October 2006 the WikiLeaks.org domain was registered. Julian Assange’s biological father John Shipton was also listed as a registered holder of the domain.
*
During 2006, Assange also approached John Gilmore, co-founder of both the cypherpunks and the Electronic Frontiers Foundation (EFF), who agreed the latter organisation “should consider helping”. Danny O’Brien from EFF contacted Assange to offer legal advice, contacts and other resources.
Not everybody wanted to get involved. Assange went to visit Ben Laurie, a prominent British computer security expert, who said it was a brilliant idea but: "Who would be insane enough to contribute stuff?" Although he didn’t think Julian’s plan would work, Laurie agreed to be on the Advisory Board.
The famous US whistle-blower Daniel Ellsberg, who leaked the Pentagon Papers in 1971, also received an anonymous email signed “WL”.
Dear Mr. Ellsberg.
We have followed with interest and delight your recent statements on document leaking. We have come to the conclusion that fomenting a world wide movement of mass leaking is the most cost effective political intervention available to us* We believe that injustice is answered by good governance and for there to be good governance there must be open governance. Governance by stealth is governance by conspiracy and fear. Fear, because without it, secrecy does not last for long. Retired generals and diplomats are vociferous, but those in active service hold their tune.
Lord Action said, "Everything secret degenerates, even the administration of justice; nothing is safe that does not show how it can bear discussion and publicity".
This degeneration comes about because when injustice is concealed, including plans for future injustice, it cannot be addressed. When governance is closed, man’s eyes become cataracts. When governance is open, man can see and so act to move the world towards a more just state; for instance see http://en.wikipedia.org/wiki/Reporters_Without_Borders which shows a striking correlation between press freedom and countries known for their quality of life.
us*: some attributes may have been swapped to protect selected identities, no particular order.
1) Retired new york architect and notorious intelligence leak facilitator 2) Euro cryptographer/programmer 3) Pacific physicist and illustrator 4) A pacific author and economic policy lecturer 5) Euro, Ex-Cambridge mathematician/cryptographer/programmer 6) Euro businessman and security specialist/activist 7) Author of software than runs 40% of the world’s websites. 8) US pure mathematician with criminal law background 9) An infamous US ex-hacker 10) Pacific cryptographer/physicist and activist 11) US/euro cryptographer and activist/programmer 12) Pacific programmer 13) Pacific architect / foreign policy wonk
New technology and cryptographic ideas permit us to not only encourage document leaking, but to facilitate it directly on a mass scale. We intend to place a new star in the political firmament of man. We are building an uncensorizable branch of Wikipedia for leaked documents and the civic institutions & social perceptions necessary to defend and promote it. We have received over 1 million documents from 13 countries, despite not having publicly launched yet!
We have approached you now for two reasons. Firstly, we have crossed over from `prospective' to `projective'. The basic technology has been prototyped and we have a view as how we must proceed politically and legally. We need to move and inspire people, gain volunteers, funding, further set up the necessary political-legal defenses and deploy. Since you have thought about leaking more than anyone we know, we would like you on board. We’d like your advice and we’d like you to form part of our political armor. The more armor we have, particularly in the form of men and women sanctified by age, history and class, the more we can act like brazen young men and get away with it.
Secondly, we would like to award "The Ellsburg Prize for Courageous Action" and "The Ellsburg Prize for Courageous Action (USA)", for the two leaks submitted in the past year which most assist humanity. The regionalization of the second prize is to encourage patrons of similar awards in other countries. Although it is premature to go into detail, we have designed a scheme were this can be meaningfully awarded to anonymous leakers. We have been pledged substantial initial funding.
Please tell us your thoughts. If you are happy, we will add you to our internal mailinglist, contacts, etc. Solidarity! WL.
Ellsberg, who later became a strong supporter, politely turned down the offer:
“Your concept is terrific and I wish you the best of luck with it.”
*
Those who agreed to help eventually received the following email from Assange, where the name “WikiLeaks” was first spelled out:
"This is a restricted internal development mailing list for w-i-k-i-l-e-a-k-s-.-o-r-g. Please do not mention that word directly in these discussions; refer instead to 'WL'. This list is housed at riseup.net, an activist collective in Seattle with an established lawyer and plenty of backbone."
The original idea was that the website would function as a wiki, with users able to log on, analyse data and share their findings.
|
Note
|
The term “wiki” refers to a collaborative website, where many users can contribute and edit content, which is how the WikiLeaks site originally functioned. The name WikiLeaks was partly inspired by the growing success of Wikipedia, the online collabarative encyclopedia, which was also built on free public "wiki" software and became one of the world’s top 10 websites in 2007. The two sites have nothing else in common. |
*
By the end of 2006 Assange was writing prolifically on his blog. On December 3 2006 he posted a 6 page PDF document called Conspiracy as Governance:
To radically shift regime behavior we must think clearly and boldly for if we have learned anything, it is that regimes do not want to be changed. We must think beyond those who have gone before us and discover technological changes that embolden us with ways to act in which our forebears could not.
We must understand the key generative structure of bad governance.
We must develop a way of thinking about this structure that is strong enough to carry us through the mire of competing political moralities and into a position of clarity. Most importantly, we must use these insights to inspire within us and others a course of ennobling and effective action to replace the structures that lead to bad governance with something better.
The document includes a key visualisation of how information leaks can break down complex conspiracies:
First take some nails (“conspirators”) and hammer them into a board at random. Then take twine (“communication”) and loop it from nail to nail without breaking. Call the twine connecting two nails a link. Unbroken twine means it is possible to travel from any nail to any other nail via twine and intermediary nails. Mathematicians say that this type of graph is connected.
Information flows from conspirator to conspirator. Not every conspirator trusts or knows every other conspirator even though all are connected. Some are on the fringe of the conspiracy, others are central and communicate with many conspirators and others still may know only two conspirators but be a bridge between important sections or groupings of the conspiracy…
Imagine a thick heavy cord between some nails and fine light thread between others. Call the importance, thickness or heaviness of a link its weight. Between conspirators that never communicate the weight is zero. The “importance” of communication passing through a link is difficult to evaluate a priori, since its true value depends on the outcome of the conspiracy. We simply say that the “importance” of communication contributes to the weight of a link in the most obvious way; the weight of a link is proportional to the amount of important communication flowing across it.
On December 31 2006 Assange summarized his thoughts in a short blog post called The non linear effects of leaks on unjust systems of governance:
“The more secretive or unjust an organization is, the more leaks induce fear and paranoia in its leadership and planning coterie. This must result in minimization of efficient internal communications mechanisms (an increase in cognitive "secrecy tax") and consequent system-wide cognitive decline resulting in decreased ability to hold onto power as the environment demands adaption.
“Hence in a world where leaking is easy, secretive or unjust systems are nonlinearly hit relative to open, just systems. Since unjust systems, by their nature induce opponents, and in many places barely have the upper hand, mass leaking leaves them exquisitely vulnerable to those who seek to replace them with more open forms of governance.
“Only revealed injustice can be answered; for man to do anything intelligent he has to know what’s actually going on.”
*
By this time, rumours about the new WikiLeaks site were swirling online. Some of those involved were impatient to launch the website while others urged patience. An internal email stated:
In relation to timing; We intend to go live with a reduced system in the next month. Untill then we are publishing selected analysis in convential venues to get some material out and encourage assistance. We’re gradually scaling up. At the moment we have certain asymmetries- e.g more leaks than we can store or index. It’s just a matter of gradually inspiring increasing commitment and resources from generous people.
But in an ironic twist that would be repeated several times in years to come, news about WikiLeaks was prematurely leaked. Britain’s New Scientist magazine started revealing details at the end of December 2006, for a story to be published in early 2007. The Associated Press was also working on a story. And the WikiLeaks website still was not even live.
*
*
The author of this book can be found on Twitter: @Jaraparilla
*
Home - Genesis - 2007 - 2008 - 2009 - Early 2010 - Mid 2010 - Late 2010 - End 2010 - Early 2011 - Mid 2011 - Late 2011 - End 2011 - Early 2012 - Late 2012 - Early 2013- Late 2013 - 2014 - 2015 - Early 2016 - Late 2016 - 2017-19
Copyright Gary Lord 2021, 2022, 2023